What about security in IoT and IIoT?

As per the results, 99% of security professionals have difficulty verifying the safety of their Internet of Things (IoT) and industrial internet (IIoT) equipment, and 95% are concerned about the hazards presented by these connected devices. The results of the survey show that:
Internet of Things and Industrial Internet of Things (IIoT) security
Connected devices don't readily fit into the security strategy of more than three-quarters of respondents, and 88 percent need extra resources to address IoT and IIoT security demands. Both of these figures show that more study and development are required in this area. 53 percent of respondents said they could not monitor linked devices entering their controlled environment, and 61 percent had little insight into changes in the security providers that were part of their supply chain.
Concerns and practices of security experts who are responsible for the connected environment's security
According to the reports that are coming out every week, there has been an unprecedented number of large-scale data breaches at a corporation that was formerly considered immune to such attacks. Firms that have used or stored personal data in ways that were not intended by the persons or organizations that provided it also cause concern. Because of this, the problem might become worse before it gets better as more gadgets are introduced.
Some of the most common security issues in Industrial Internet of Things networks will be discussed here, along with remedies for these flaws.
As a result of Our Journey
When trying to comprehend how Industrial IoT ended up in this situation, there are two main elements to keep in mind. There is basic math involved in the first one. Service providers are under increasing pressure to provide devices and platforms ready for deployment, which puts them in danger of doing more than security efforts and protocols can manage.
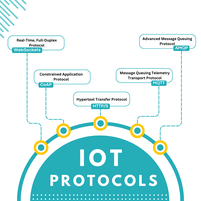
One explanation is that similar problems have arisen with previous groundbreaking technologies that have been very successful. In other words, security has never before had to be handled at the machine level. Standardization and protocol development stalled as a consequence. As a result, providers either dealt with them on an ad hoc basis, used the third-party security provider that the customer had picked, or even relied entirely on the client's internal security processes.
Sites with a high potential for criminal activity
A data breach is more likely now that hackers use the same data tools and artificial intelligence technology that IoT system developers use. It is possible to enter a factory and the systems that are connected via a variety of ways, including the following:
There are several issues with IoT devices' web interfaces, including inadequate default passwords, lockout and session management problems, and credential leakage in the network. It is possible that several variables are to blame for these issues.
Mobile Devices with Insecure User Interfaces Field service as an extension of a company's manufacturing activity is becoming more common, particularly for the purposes of repair and maintenance. As with desktop computers, mobile interfaces are susceptible to the same issues of encryption and authentication.
IIoT Security Issues and Solutions
There is a high demand for IoT providers that provide both services and devices since many firms have security measures in place that are weak or insufficient. Microsoft's obsolete software is used in more than half of all operations at critical infrastructure sites, and 40% of all industrial facilities are connected to the internet openly.
If a good hacker gains access to a whole facility, they might delay or completely halt production for a lengthy period. This makes machine penetration a crucial worry as gadgets continue to increase. The intrusion may lead to circumstances where people are in danger of being hurt, either directly or indirectly.
Another issue that has to be addressed is the safety of heirlooms. The Industrial Internet of Things has a significant benefit because older gear may be retrofitted with IoT devices. As a result, equipment lifecycles may be prolonged, and the systems can be fully integrated to create an intelligent factory without needing large-scale capital equipment purchases. A careful analysis of which devices can be effectively safeguarded for use in the system is required before making a choice. If a company doesn't have this skill, it may not recognize it needs one until it's too late.
The lack of standards and norms in an industry still in its infancy but growing exponentially is another aspect that is dragging down the development of coherent security innovation. According to most experts, service providers in the IoT industry will join together and self-regulate to develop universal standards and norms for all projects.
A Joint Effort in the Workplace
Industrial Internet of Things Security Solutions
More than 40% of all exploited security flaws are the result of malware and brute force assaults. But there are many more ways for someone to intrude on your personal space. There are four main layers of security: device, communication, cloud, and lifecycle management. This is because there are so many possible access points to a company's appliances and systems. Due to the fast expansion of the industry, security solutions have grown increasingly complex to adopt; today, there is no ready-made, end-to-end solution.
While end-to-end solutions are being developed, service providers and enterprises may take specific interim measures.
One of these stages would include segmenting the IT network to separate the equipment control network from the rest of the company's IT infrastructure.
Second, service providers may ensure the "fundamentals" on their own. Basic precautions, like default credentials that must be changed upon activation and credential lockout after a specific number of unsuccessful login attempts, may help protect the web interface. Similarly, two-factor authentication and vital password requirements may be used to prevent unauthorized access.
You may remove possible entry points in information technology by preventing services from being vulnerable to buffer overflow and blocking ports when they are not in use. Mobile devices' user interfaces may include the same security features, such as password, lockout, and default password rules. System degradation may be reduced through a more rigorous approach to manufacturing and deploying firmware upgrades.
Developing industry standards and processes is one of the most critical actions that the sector can take to stay ahead of security issues. This is the most important action that can be taken. By standardizing and mandating the inclusion of a base architecture for many of the issues listed above, service providers and the programming teams they employ would be liberated from the more inconsequential security concerns. They could concentrate on the larger and more complex security concerns as they develop.
The number of security issues that will arise as a result of the Internet of Things is expected to rise.
Industrial Internet of Things service providers and businesses that employ these services face increasingly complicated security challenges. Many individuals don't give much thought to safety, yet they're missing out on chances because of it. More and more corporate executives have said that they are willing to pay more for Internet of Things (IoT) devices and services if they include security solutions. New services that integrate security into the platform or have strong partnerships with third-party security providers will likely gain traction in the market as the sector grows. These innovative offerings will achieve a competitive advantage.
Explore more
Need any help in IoT?
Need any help in IoT? An Atreyo expert identify the right solution for your needs.
If ready to talk to an Atreyo expert
Interested in IoT products? go to